Find out what risks you are facing, using our easy and fast risk Intel threat checker! Read More
Datenverstoß in der Sandbox
Die letzten Tage waren gelinde gesagt interessant, der Bundestag wurde wieder einmal gehackt und niemand weiß mehr als vorher. Mit all den fake News und Berichten ist es sehr schwer zu unterscheiden, was an diesem neuen Verstoß real ist und was nicht, oder ob es wirklich ein neuer Verstoß war. Was wir beobachten, ähnelt einer… Read More
Data Breach in the Sandbox
The last few days have been interesting to say the least, the Bundestag got hacked once again and no one is the wiser. With all the “fake” news and reports its very hard to distinguish what is and isn’t real about this new breach or even if it was really a new breach. What we… Read More
Operation KRAKEN Strikes Again!
Lesen Sie diesen Artikel in Deutsch hier ~ Read this in German here. See also: “Operation KRAKEN” published in September 2018 Friday, 4th of January ~ When I presented at the Bundestag in Berlin on multiple occasions about cyber security, we gave them our information for free with a warning. That warning was that their… Read More
Threat and risk profiling and detection
Today’s attackers are more sophisticated and complex, you need to be one step ahead without constant manual effort. Read More
IOT and cyber threat detection
Attackers can use IoT to break into your home or company. Don’t let them! Read More
Malware discovery and analysis
Only proactive and dynamic automated defenses can be successful Read More
Cyber Espionage Detection
Cyber Crime, Warfare and Espionage – do you know the difference? Read More
True Cost of Software Errors
346 people died because of software issues, if we invest in secure code, testing and security in development then maybe those 346 people would not have died in 2 plane crashes. Read More
CRisk Framework
We are introducing another giant step in OSINT and Cyber Risk Intelligence by introducing our own CRisk Framework. Read More
FaceTime Terrorism
A previously unpublished FaceTime bug allows attackers to record your discussions without your knowledge. Read More
Simply Undetectable
As this year (2019) starts to mature we are and will see more and more attacks that target SMB’s (Small and Medium Businesses) and also larger corporations in ways that (currently) classical security teams are not prepared for. Why do I say this, is it some sales ploy or an attempt at creating fear? Actually… Read More
Why bank groups trust us with their IT security
Making money one way or another is one of the major reasons, if not the most important reason, for cyber-attacks and cybercrime. Banks accordingly are prime targets for cyber adversaries and must deal with all sorts of different risks and attacks. The Federal Reserve Bank of Cleveland has put together a high-quality summary of those… Read More
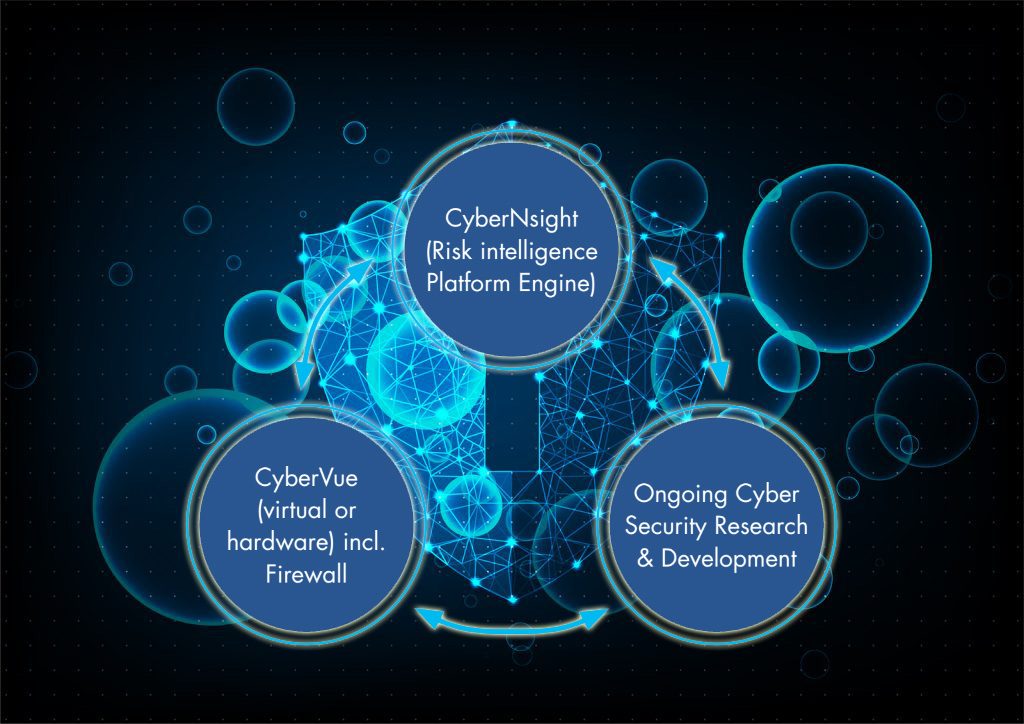
Risk Intelligence with Analysis in Real Time
Use cases with CyberNsight I wanted to talk about what we are doing to stop unknown malware and threats as well as risks from turning into fines for customers or worse stolen IP and or data of customers, contracts, research or any relevant value in the form of a given asset type. I said before… Read More
Docker Bug: Firewall workaround…
Published December 2018 We wanted to put out a Bug Info for newer Docker installations that interact with MongoDB. Due to changes in how Docker does its routing it and in some cases ignores IPChains and Firewall settings in certain situations that leads to your MongoDB schema and data being accessible with a MongoDB client… Read More